How to Install OpenClaw on a UGREEN NAS & Setup Your AI Assistant
UGREEN NAS and OpenClaw – How to Install it, Setup Your AI and Understanding The Risks!
OpenClaw has now moved from a manual self-hosted setup into the UGREEN UGOS Pro App Center, making it possible to install the assistant gateway directly on supported UGREEN NASync systems rather than building it manually through a VM, terminal commands, or a separate always-on PC. In practical terms, OpenClaw is not the AI model itself. It is the local assistant layer that connects your NAS, files, tools, skills, and messaging channels to an LLM such as OpenAI, Gemini, DeepSeek, MiniMax, OpenRouter, or a local model where supported. This matters because a NAS is where many users already keep their long-term data, backups, media, documents, and project files, but it also means OpenClaw needs to be treated as a privileged automation tool rather than a simple chatbot. The App Center version lowers the installation barrier, but the real value and the real risk both come from what you allow it to access, what model you connect it to, and which skills or messaging channels you enable.

Security Considerations Before Giving OpenClaw NAS Access
OpenClaw should be approached as a privileged automation layer, not as a normal chat assistant. On UGREEN NAS, it runs through Docker and is designed to read, write, delete, move files, publish messages, and execute system-level operations depending on what folders, skills, and channels you enable. UGREEN’s own notes state that the application runs inside a Docker container with root privileges, which is necessary for broad automation but also increases the potential damage from incorrect commands, poor configuration, compromised plugins, or prompt-injection style attacks. The main rule before installation is therefore straightforward: do not give OpenClaw access to anything you are not prepared for it to modify, and make sure you have a working backup before testing it on real data.
The risks increase further if you connect OpenClaw to a remote LLM provider or public messaging platform. When using OpenAI, Gemini, MiniMax, DeepSeek, OpenRouter, or similar services, your prompts, file context, directory details, task instructions, logs, or extracted content may be sent outside the NAS depending on the action being performed. OpenClaw’s own GitHub description warns that real messaging surfaces should be treated as untrusted inputs, and recent reporting has also highlighted malicious third-party OpenClaw skills that attempted to steal credentials, wallet data, and browser information. For NAS use, the safest starting point is to use a test folder, avoid private or business-critical data, do not expose the service directly to the public internet, install only trusted skills, and treat WhatsApp, Telegram, Discord, Slack, or similar integrations as external access points into your NAS assistant.

Preparing Folders and Installing OpenClaw from UGOS Pro
Before installing OpenClaw, create the folders it will use and decide how much of the NAS it should be allowed to see. In Files, either create a dedicated shared folder or a personal folder for OpenClaw’s workspace, for example openclaw-data or openclaw-workspace. This should ideally be an empty folder, as it will be used for temporary files, generated content, working data, and task execution. Separately, create or identify the folder that OpenClaw will be allowed to access for real NAS file operations. For first-time testing, this should be a limited test directory rather than a folder containing live backups, sensitive documents, business files, or irreplaceable media. The workspace path and file access path should not overlap, and the access path should not sit inside the workspace folder. UGREEN also notes that Docker should be installed and updated first, as OpenClaw relies heavily on the Docker container environment.

Once the folders are ready, open App Center in UGOS Pro, find OpenClaw under the app list, and select Install. During the installation wizard, set the Workspace path to the empty folder created for OpenClaw’s internal working area, then set the File access path to the NAS folder or folders that the assistant is permitted to read or modify. Multiple access paths can be added, but this should be done deliberately, as these paths define the practical scope of what OpenClaw can act on. Next, create a Gateway token, which will be required when signing in to the OpenClaw web interface. After reviewing the risk notice, tick the confirmation box and start the installation. The package is installed through the App Center, but it still deploys and runs through Docker in the background, so installation time will depend on NAS performance, internet connection speed, and the state of the Docker environment. OpenClaw’s own Docker documentation also describes the gateway token and container-based control UI as central parts of the deployment model.

Point-by-point setup:
- Open Files in UGOS Pro.
- Create an empty folder for the OpenClaw workspace, such as
openclaw-workspace. - Create a separate test folder for OpenClaw file access, such as
openclaw-test-data. - Avoid selecting folders that contain private, business-critical, backup, password, financial, or personal archive data.
- Open App Center.
- Confirm Docker is installed and updated.
- Search for OpenClaw under the app list.
- Click Install.
- Set the Workspace path to the empty OpenClaw working folder.
- Set the File access path to the limited folder OpenClaw can manage.
- Add additional access paths only if they are required.
- Create and record a Gateway token.
- Read the installation risk notice.
- Tick the confirmation box.
- Click Install and allow the deployment to complete.

Linking OpenClaw to an AI Model Provider
OpenClaw needs an AI model before it can act as an assistant. The UGREEN App Center installation can collect model details during setup, but these can also be managed later from the OpenClaw console under Model providers. The information required is usually the same across providers: a base URL or request endpoint, a model name, and an API key.

OpenAI’s current API reference lists https://api.openai.com/v1 as the standard API base, with chat completions available under /chat/completions, while Google documents Gemini’s OpenAI-compatible endpoint as https://generativelanguage.googleapis.com/v1beta/openai/. These details matter because a wrong endpoint, wrong model name, or invalid key will usually result in provider errors inside OpenClaw rather than a NAS-side installation problem.

For a UGREEN NAS setup, most users will start with a remote model provider such as OpenAI, Google Gemini, DeepSeek, MiniMax, Groq, OpenRouter, or another OpenAI-compatible API. iDX models with local AI model support may also allow local model use, but that depends on the local model service exposing a usable API endpoint and key.

A remote model is easier to configure, but it can send task instructions, file context, extracted text, and other prompts outside the NAS. A local model reduces this dependency, but it may require more RAM, more setup, and a compatible local inference service. OpenClaw supports model provider configuration and key rotation through its own provider system, so the NAS app should be treated as the deployment layer rather than the only place where model behaviour can be managed.

Point-by-point setup:
- Open the OpenClaw shortcut from the UGREEN NAS desktop.
- Sign in using the Gateway token created during installation.
- Go to Model providers in the left-side menu.
- Click Add provider.
- Select the provider you want to use, such as OpenAI, Google Gemini, DeepSeek, MiniMax, or another supported provider.
- Enter the provider’s Base URL or full API endpoint.
- Enter the required API key from the provider’s developer console.
- Enter or select the Model name that matches the provider’s supported model ID.
- Save the provider configuration.
- Go to the Default model area.
- Select the model OpenClaw should use by default.
- Click Save to apply the default model.
- Open Chat and send a basic test prompt, such as
What model are you running on? - If OpenClaw returns a provider error, check the API key, model name, endpoint format, account billing status, and provider rate limits.
- If using a local model on an iDX system, use the local service IP address and port as the base URL rather than a public cloud endpoint.

Common examples:
| Provider | Typical API Base URL |
|---|---|
| OpenAI | https://api.openai.com/v1 |
| OpenAI Chat Completions request path | https://api.openai.com/v1/chat/completions |
| Google Gemini OpenAI-compatible endpoint | https://generativelanguage.googleapis.com/v1beta/openai/ |
| DeepSeek | https://api.deepseek.com |
| Groq | https://api.groq.com/openai/v1 |
| OpenRouter | https://openrouter.ai/api/v1 |
| MiniMax | https://api.minimax.chat/v1 |

Opening the OpenClaw Console and Testing the Assistant
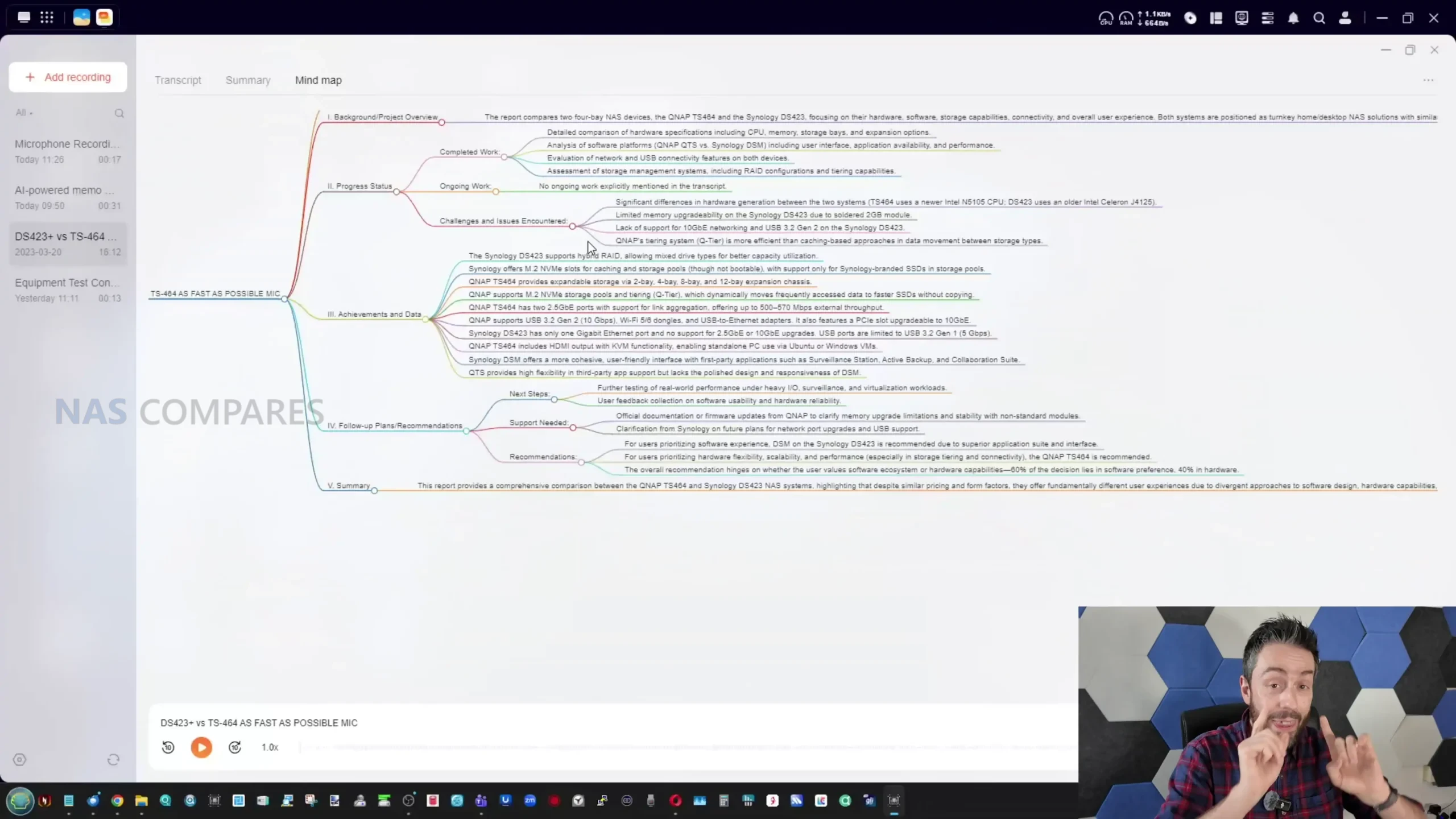
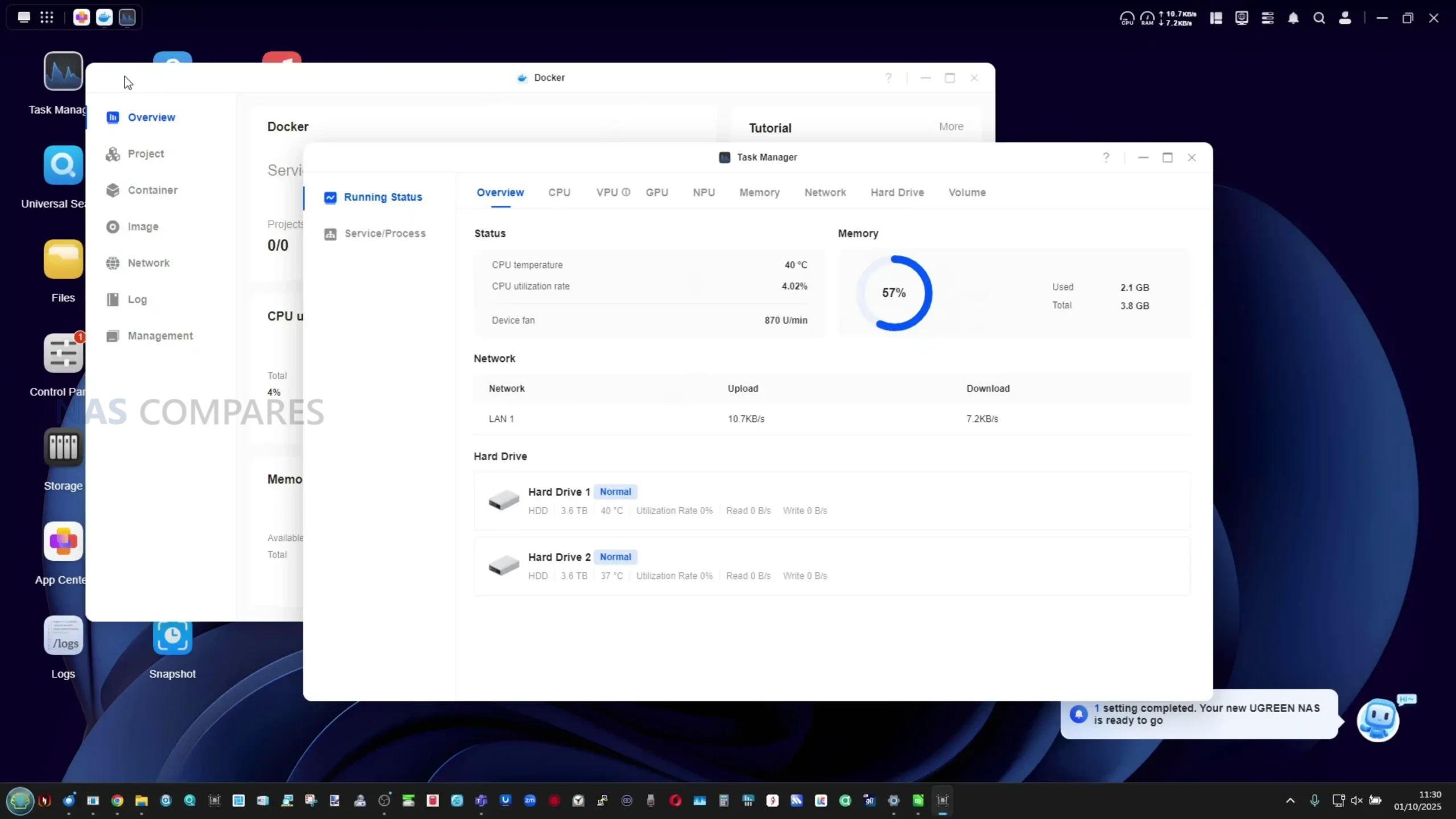
Once installation and model configuration are complete, OpenClaw can be launched from the UGREEN NAS desktop. Clicking the OpenClaw shortcut opens the web console in a browser, where the first prompt will ask for the Gateway token created during installation. After signing in, the Overview page shows whether the gateway is active, along with container runtime details such as uptime, CPU usage, memory usage, gateway port, process information, and overall service status. If the service is running correctly, the status area should show an active or healthy state, and the Open OpenClaw button can be used to launch the native OpenClaw interface in a new browser tab.

The first test should be simple. Open the Chat page, send a basic message, and confirm that the configured model responds. After that, test only against the limited folder path selected during setup. For example, ask it to list files in the permitted test directory, create a new folder inside it, or summarize a non-sensitive test document. This confirms that OpenClaw, the model provider, and the NAS file permissions are all working together. If the model does not respond, check the model provider settings first. If file actions fail, check that the command references the correct mounted path shown in the OpenClaw app configuration rather than a folder name as displayed in the normal UGREEN Files interface.

Point-by-point setup:
- Open the OpenClaw shortcut from the UGREEN NAS desktop.
- Enter the Gateway token.
- Click Sign in or Connect.
- Open Overview.
- Confirm the service status is active.
- Check the runtime snapshot for CPU usage, memory usage, and uptime.
- Click Open OpenClaw if you want to use the native OpenClaw interface.
- Open Chat from the left-side menu.
- Send a basic test message, such as
Hello. - Ask which model is active, for example
What model are you using? - Test file access only inside the approved test folder.
- Use a low-risk command, such as
Create a folder called OpenClaw Test in [your mounted test path]. - Open Files in UGOS Pro and confirm the folder was created.
- If the command fails, check the actual accessible path under Control Panel > About > Apps > OpenClaw.
- Review Operation Logs if OpenClaw responds incorrectly, fails to access files, or reports a gateway or provider error.

Choosing Skills and Plug-ins for NAS-Based Use
OpenClaw skills and plug-ins extend what the assistant can do beyond basic chat. In a NAS environment, these additions should be chosen more cautiously than they might be on a laptop or test VM, because a skill may request access to files, shell commands, browser sessions, messaging platforms, or external services. OpenClaw’s public site describes it as an assistant that can act through channels such as WhatsApp, Telegram, and other chat apps, while community skill indexes now list thousands of available skills. That breadth is useful, but it also means the skill ecosystem should not be treated as automatically safe or suitable for storage systems. (openclaw.ai, clawskills.sh)

For a UGREEN NAS, the sensible starting point is to enable only the skills that match a specific NAS task. File management, system monitoring, web browsing, document parsing, OCR, and basic notification workflows are the most relevant categories. Avoid installing skills that request broad shell access, browser credential access, crypto wallet access, password manager access, or unclear third-party scripts unless they have been reviewed carefully. This is not theoretical. Reports in early 2026 documented malicious OpenClaw skills that attempted to steal browser data, SSH credentials, wallet information, and other sensitive data, which is particularly relevant when the assistant is being installed on a machine that stores personal or business files.

Point-by-point setup:
- Open the OpenClaw console from the UGREEN NAS desktop.
- Sign in with the Gateway token.
- Open the native OpenClaw interface using Open OpenClaw, if required.
- Go to the Skills, Plug-ins, or Skills Store area.
- Search for skills by function rather than installing large bundles.
- Start with NAS-relevant categories only.
- Check the skill description, source, permissions, and install method.
- Avoid any skill that asks you to run unclear terminal commands.
- Install 1 skill at a time.
- Test it only against the approved OpenClaw test folder.
- Check Operation Logs after each test.
- Remove any skill that behaves unexpectedly or asks for broader permissions than needed.
- Avoid using “always allow” approvals until the workflow has been tested repeatedly.
- Keep a note of which skills are installed and what each one can access.
- Review installed skills periodically, especially after OpenClaw or UGOS Pro updates.

Recommended NAS-related starting points:
| Skill or plug-in type | NAS use case | Notes |
|---|---|---|
| File management | Create folders, move files, rename files, list directory contents | Use only on approved test paths at first |
| System monitoring | Ask for runtime status, resource usage, uptime, container state | Useful for checking OpenClaw and NAS load |
| Web browsing | Fetch public information, check release notes, compare documentation | Avoid entering NAS credentials into automated browser sessions |
| Document parsing | Summarize PDFs, text files, logs, notes, or project documents | Use non-sensitive documents until behaviour is confirmed |
| OCR or image analysis | Extract text from screenshots, scans, and captured images | Useful for receipts, manuals, and screenshots stored on NAS |
| Notification or messaging | Send alerts to chat platforms when a task completes | Keep access limited and avoid exposing private file contents |
| Calendar or reminders | Create simple task reminders or schedule follow-up actions | Only connect accounts you are comfortable granting access to |
| GitHub or code repository tools | Track updates, commits, issues, or project notes | Relevant for developer or homelab use, less important for general storage |
| Shell or terminal tools | Advanced maintenance and automation | High risk; avoid unless you know exactly what commands may be run |
| Database query tools | Query structured local datasets or app databases | Use read-only credentials where possible |
Connecting OpenClaw to WhatsApp, Discord, and Telegram
OpenClaw can be used through external messaging platforms so that commands can be sent to the NAS assistant without opening the UGREEN web interface each time. The supported channel list includes WhatsApp, Telegram, Discord, Slack, Google Chat, Signal, Microsoft Teams, Matrix, Feishu, LINE, Mattermost, Nextcloud Talk, and others, but WhatsApp, Telegram, and Discord are likely to be the most relevant for home and small-office users. OpenClaw’s own channel notes state that multiple channels can run at the same time, but they also warn that inbound messages should be treated as untrusted input and that DM pairing or allowlists are used for access control. (github.com, docs.openclaw.ai)

For NAS use, Telegram is usually the simplest starting point because it relies on a bot token from BotFather. WhatsApp normally uses QR pairing and stores more session state on disk, which means it may need more care during backups, container resets, or reinstallation. Discord is more useful when OpenClaw needs to operate inside a server, channel, or team context, but it should be restricted to private channels and trusted roles rather than broad server-wide access. The UGREEN console provides a channel management area where plugins can be enabled, configured, and monitored, but more advanced channel setup may still require working inside the OpenClaw interface or Docker container depending on the platform and plugin. (docs.openclaw.ai, openclaw-openclaw.mintlify.app)
Point-by-point setup:
- Open the OpenClaw console from the UGREEN NAS desktop.
- Sign in using the Gateway token.
- Go to Channels.
- Select the channel you want to enable, such as Telegram, WhatsApp, or Discord.
- Click Enable for the required channel plugin.
- Wait until the plugin status changes to Ready.
- Click Add channel.
- Enter the required account, bot, or pairing details.
- Configure DM access rules, pairing mode, or allowlist behaviour where available.
- Bind the channel to the correct OpenClaw agent or default assistant.
- Send a low-risk test message from the external app.
- Confirm that OpenClaw replies through the same channel.
- Test with a harmless NAS action inside the approved test directory only.
- Check Operation Logs if messages are received but not answered.
- Disable the channel if unexpected users, groups, or servers can trigger the assistant.

Telegram setup:
- Open Telegram.
- Search for @BotFather.
- Create a new bot using
/newbot. - Copy the bot token provided by BotFather.
- Return to OpenClaw > Channels.
- Enable the Telegram plugin.
- Add a Telegram channel.
- Paste the bot token.
- Configure whether the bot can respond in DMs, groups, or both.
- Send a test message to the bot.
WhatsApp setup:
- Open OpenClaw > Channels.
- Enable the WhatsApp plugin.
- Add a WhatsApp channel.
- Enter the phone number or pairing account details requested by the setup window.
- Generate the QR pairing code.
- Open WhatsApp on your phone.
- Go to linked devices.
- Scan the QR code.
- Wait for the WhatsApp channel status to become active.
- Send a test message to confirm OpenClaw responds.
Discord setup:
- Create or use a Discord server where you control permissions.
- Create a dedicated private channel for OpenClaw commands.
- Create a Discord bot in the Discord Developer Portal.
- Copy the bot token.
- Return to OpenClaw > Channels.
- Enable the Discord plugin.
- Add a Discord channel.
- Paste the bot token.
- Restrict the bot to trusted channels and roles.
- Send a test command in the private OpenClaw channel.

UGREEN x OpenClaw: Useful, but Only with Controlled Access
OpenClaw on UGREEN NAS is a notable step towards making AI-assisted NAS management more accessible, mainly because the App Center version removes much of the older manual deployment work. Instead of installing Ubuntu in a VM, configuring Node.js, running installation scripts, and manually binding the gateway, supported UGREEN NASync users can now install OpenClaw through UGOS Pro and complete the main path, token, and model setup through a guided interface. That makes the initial process easier, but it does not make OpenClaw a basic consumer NAS feature. It is still an automation agent with access to files, tools, model providers, messaging channels, and potentially system commands.

The value depends on how tightly it is configured. Used against a limited folder, with a known model provider, a small number of trusted skills, and private messaging channels, OpenClaw can help with file organisation, document handling, system checks, reminders, and assistant-style NAS interaction. Given broad storage access, untested skills, exposed web access, or remote AI services without understanding the data flow, it becomes a much higher-risk deployment. For most users, the best approach is to begin with a test directory, avoid sensitive data, keep backups current, and expand access only after confirming exactly how OpenClaw behaves in day-to-day use.
Want to Support the work me and Eddie do at NASCompares? If you found this article helpful and are going to buy a UGREEN NAS from the brand’s official site or from Amazon, use the links below. Using these links will result in a small commission coming to us (which costs you nothing extra) and it allows us to keep doing what we do! Thank you for keeping the internet a fair and sustainable place!
| Buy the UGREEN NAS from your local Amazon Store | Buy the UGREEN NAS solutions Directly from UGREEN.COM |
 |
 |
 SUBSCRIBE TO OUR NEWSLETTER
SUBSCRIBE TO OUR NEWSLETTER 
[contact-form-7]
 Join Inner Circle
Join Inner Circle
Get an alert every time something gets added to this specific article!
 Subscribe
Subscribe
This description contains links to Amazon. These links will take you to some of the products mentioned in today's content. As an Amazon Associate, I earn from qualifying purchases. Visit the NASCompares Deal Finder to find the best place to buy this device in your region, based on Service, Support and Reputation - Just Search for your NAS Drive in the Box Below
Need Advice on Data Storage from an Expert?
Finally, for free advice about your setup, just leave a message in the comments below here at NASCompares.com and we will get back to you. Need Help?
Where possible (and where appropriate) please provide as much information about your requirements, as then I can arrange the best answer and solution to your needs. Do not worry about your e-mail address being required, it will NOT be used in a mailing list and will NOT be used in any way other than to respond to your enquiry.
[contact-form-7]
Need Help?
Where possible (and where appropriate) please provide as much information about your requirements, as then I can arrange the best answer and solution to your needs. Do not worry about your e-mail address being required, it will NOT be used in a mailing list and will NOT be used in any way other than to respond to your enquiry.
[contact-form-7]
 Ko-fi or old school Paypal. Thanks!To find out more about how to support this advice service check HEREIf you need to fix or configure a NAS, check Fiver
Have you thought about helping others with your knowledge? Find Instructions Here
Ko-fi or old school Paypal. Thanks!To find out more about how to support this advice service check HEREIf you need to fix or configure a NAS, check Fiver
Have you thought about helping others with your knowledge? Find Instructions Here

|
 |




.webp)


.webp)














.webp)
