Vue lecture
Adversaries Exploit Vacant Homes to Intercept Mail in Hybrid Cybercrime
ThreatsDay Bulletin: Pre-Auth Chains, Android Rootkits, CloudTrail Evasion & 10 More Stories

À 36 000 km de la Terre, l’incroyable course d’Artémis II dans le ciel

La fusée SLS a décollé dans la nuit du 1er au 2 avril 2026 pour lancer la mission historique Artémis II. Si les objectifs des photographes l'ont mitraillée depuis le sol, le point de vue le plus vertigineux nous vient de l'espace. À près de 36 000 km de distance, un satellite météorologique a capturé une trace étonnante de ce départ vers la Lune.
« Première mondiale » : la France et le Japon réussissent un chiffrement inédit basé sur l’ADN

Une équipe franco-japonaise affirme avoir réussi, pour la première fois en conditions réelles, à chiffrer et déchiffrer des données à partir d’ADN. Présentée par Emmanuel Macron le 1er avril 2026, cette démonstration explore une nouvelle voie pour la cryptographie.
Dark Maul n’en a pas fini avec ses envies de vengeance contre tout le monde

Héros de la future série télévisée Shadow Lord (Seigneur de l'ombre), Dark Maul reviendra par la suite dans une nouvelle saison. Lucasfilm a officialisé une suite, alors que les premiers épisodes n'arriveront en streaming qu'à partir du 6 avril 2026.
Pourquoi le créateur de la série The Boys est « dévasté »

À quelques jours de la diffusion de la cinquième et dernière saison de The Boys, Eric Kripke a révélé que la série a un peu trop prophétisé la réalité. À son plus grand désarroi.
Les voitures chinoises, un « cancer pour l’économie » selon ce sénateur américain

Les États-Unis ont déjà mis en place plusieurs lois pour empêcher les constructeurs chinois d’entrer sur leur marché automobile. Un sénateur américain, le républicain Bernie Moreno, veut cependant aller encore plus loin.
Le vélo de ville électrique Elops 900 s’affiche à un prix imbattable chez Decathlon

[Deal du jour] Vous n’avez pas de vélo. Vous voulez un vélo ? Decathlon en propose un très bon, à un excellent prix. L'Elops 900 pour la ville baisse en ce moment de 250 €.
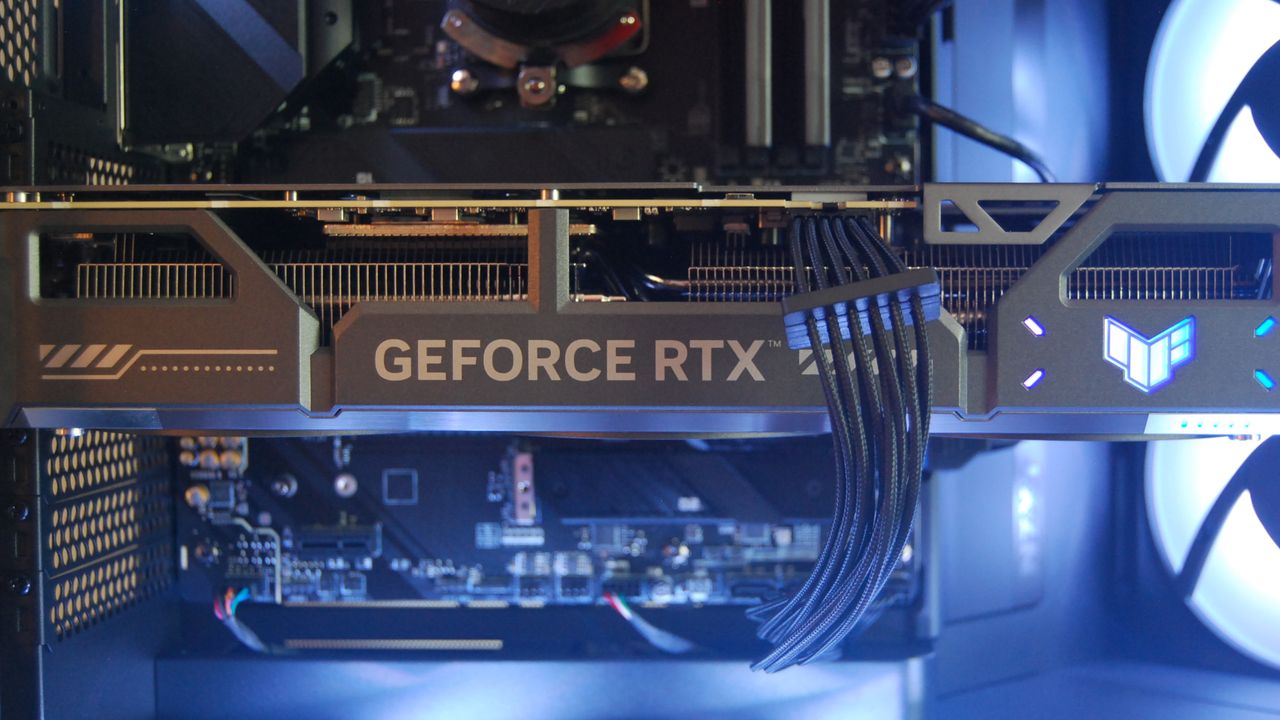
L’Arc Pro B70 en gaming, les performances progressent de 45%
 Intel a lancé ses GPU Big Battlemage dont l'Arc Pro B70. Ils visent les stations de travail mais que valent-ils en gaming ?
Intel a lancé ses GPU Big Battlemage dont l'Arc Pro B70. Ils visent les stations de travail mais que valent-ils en gaming ?
Cet article L’Arc Pro B70 en gaming, les performances progressent de 45% a été publié en premier par GinjFo.
AUO frappe fort avec un moniteur de 24 pouces en Full HD à 800 Hz
 Au Touch Taiwan 2026, AUO a dévoilé un écran gaming haut de gamme de 24 pouces Full HD capable d’atteindre les 800 Hz.
Au Touch Taiwan 2026, AUO a dévoilé un écran gaming haut de gamme de 24 pouces Full HD capable d’atteindre les 800 Hz.
Cet article AUO frappe fort avec un moniteur de 24 pouces en Full HD à 800 Hz a été publié en premier par GinjFo.
“I didn’t expect these swings”: Steam’s March survey reveals PC hardware trends that caught me off guard
The "beige cardigan" of laptops — Why Dell’s 14 Plus is a better value than its flashier rivals

Microsoft wants Edge to automatically open by default every time you turn on your Windows 11 PC
Researchers Uncover Mining Operation Using ISO Lures to Spread RATs and Crypto Miners

The State of Trusted Open Source Report

Le créateur de Resident Evil s’allie au studio de Stellar Blade et tease son nouveau projet

Shift Up, le studio sud-coréen connu pour Stellar Blade, vient de faire l’acquisition du nouveau studio fondé par Shinji Mikami, le créateur de Resident Evil et The Evil Within.
Un drone ukrainien armé d’un fusil de chasse abat un kamikaze russe en plein vol

Sur le front ukrainien, les ingénieurs de fortune ne manquent pas d'imagination. La dernière preuve en date : un drone intercepteur équipé d'un simple fusil à pompe qui parvient à neutraliser un Molniya russe dans les airs.
Crimson Desert serait-il devenu trop simple ?

Les mises à jour de Crimson Desert, déployées à un rythme frénétique depuis la sortie, auraient trop réduit le challenge de l'avis de plusieurs personnes. Elles aimeraient qu'un mode difficile soit proposé dans le jeu de Pearl Abyss.